Have you ever looked at your smartphone or laptop and felt like something was just… off? Maybe the battery died three hours earlier than usual. Perhaps the fan on your laptop sounded like a jet engine taking off, even though you only had one browser tab open. Or maybe, you noticed a strange app on your home screen that you have absolutely no memory of downloading.
If you have experienced any of these frustrating scenarios, you are not alone. But brushing these issues off as “just a glitch” or an “old battery” could be the biggest digital mistake of your life.
Welcome to 2026. The era where hackers wearing black hoodies and typing furiously in dark basements is a Hollywood myth. Today, cybercrime is a multi-billion-dollar global industry. And their primary product? Malware.
Malware (short for malicious software) is no longer designed to simply crash your computer for fun. It is designed to be invisible. It is engineered to sit quietly in the background of your devices, watching your every move, reading your text messages, recording your keystrokes, and draining your bank accounts—all while you blissfully scroll through social media.
Whether it is a terrifying Ransomware virus holding your family photos hostage, or a creepy piece of “Stalkerware” secretly installed by an ex-partner to track your GPS location, the threats are real, and they are everywhere.
But here is the good news: Malware is not magic. No matter how advanced a virus or spyware program claims to be, it is still a piece of software. And software leaves footprints. It consumes resources. It behaves in specific, predictable ways. If you know what to look for, you can catch it before the real damage is done.
In this massive, comprehensive 4,000-word master guide, we are going to pull back the curtain on modern cyber threats. We will walk you through the undeniable red flags of a malware infection on both your smartphone and your computer. More importantly, we will give you a clear, step-by-step action plan to eradicate the infection and secure your digital life for good.
Grab a cup of coffee, sit back, and let us perform a full diagnostic on your digital life.
Part 1: The Modern Landscape of Malware in 2026
Before we dive into the symptoms of an infected device, it is crucial to understand exactly what you are fighting against. “Malware” is an umbrella term. Just like “illness” can mean anything from a mild cold to a life-threatening disease, malware comes in many different forms, each with its own dark purpose.
1. Spyware and Stalkerware: The Silent Watchers
This is perhaps the most invasive and terrifying category of malware today. Spyware does exactly what the name suggests: it spies on you. It is designed to infiltrate your phone or laptop and secretly monitor your activity. It can log every keystroke you make (capturing your passwords), take screenshots of your emails, and even activate your camera and microphone without the warning light turning on.
Stalkerware is a particularly dark branch of spyware. Unlike traditional malware created by anonymous hackers for financial gain, stalkerware is often purchased and installed by someone you know—a jealous spouse, a controlling ex-partner, or a suspicious boss. These tools are often marketed legally as “employee monitoring” or “child safety” apps, but their capabilities are abused to secretly track GPS locations, read WhatsApp messages, and listen to phone calls. If you suspect someone is tracking your physical movements, stalkerware is the likely culprit.
2. Ransomware: The Digital Hostage Situation
Ransomware is the digital equivalent of a kidnapping. If this malware infects your laptop, it acts incredibly fast. It encrypts every single file on your hard drive—your financial documents, your work projects, your irreplaceable family videos—locking them behind complex military-grade encryption.
Suddenly, your screen goes black, replaced by a ticking countdown timer and a message demanding payment in untraceable cryptocurrency (like Bitcoin) in exchange for the decryption key. In 2026, ransomware gangs have become highly organized, often operating like legitimate corporations with “customer service” desks to help victims buy crypto to pay the ransom.
3. Adware and Fleeceware: The Annoying Leeches
While not as devastating as ransomware or spyware, adware is incredibly frustrating. Its sole purpose is to bombard you with aggressive, unclosable pop-up advertisements. It hijacks your browser, changing your default search engine to a shady website, and injects ads into web pages where they do not belong.
Fleeceware is a modern mobile trend. These are apps (often flashlights, simple photo editors, or astrology apps) that look harmless but come with hidden, exorbitant subscription fees. Once installed, they charge your credit card weekly through the App Store or Google Play until you manually dig into your settings to cancel them.
4. Cryptojacking: The Silent Battery Killer
With the continued rise of digital currencies, hackers realized they did not need to steal your money directly; they could use your device’s processing power to “mine” new cryptocurrency for themselves. This is called cryptojacking. If your phone or laptop is infected with a cryptominer, the hacker uses your CPU at 100% capacity in the background. You pay for the electricity and suffer the burned-out battery, while the hacker reaps the financial rewards.
Part 2: Top 10 Universal Signs of a Malware Infection
Malware creators are smart, but they cannot break the laws of computing. When a malicious program is running in the background, it requires CPU power, RAM, and network data. By observing how your device consumes these resources, you can spot the infection.
Whether you are using an iPhone, an Android, a Windows PC, or a Mac, here are the top 10 universal red flags.
1. Severe and Unexplained Battery Drain
Your smartphone or laptop battery naturally degrades over the years. If a device is three years old, it will not hold a charge like it did on day one. However, battery degradation is a slow, gradual process.
If your battery life suddenly drops off a cliff overnight—for example, you unplug your phone at 100% at 8:00 AM, and by 11:00 AM it is at 20% despite minimal use—you have a major problem. Malware, especially spyware and cryptojackers, runs continuously in the background. It never sleeps. This constant processing activity chews through your battery life at an alarming rate.
2. The Device Runs Unusually Hot
Devices get warm when you push them to their limits. If you are playing a heavy 3D graphic video game or rendering a 4K video, your phone or laptop will naturally heat up.
But what if your device is burning hot to the touch while it is just sitting idle on your desk? Or what if your laptop’s cooling fans sound like a jet engine taking off when you only have one simple web page open? This means the processor is working overtime. If you are not the one telling the processor to work, a hidden malicious program is.
3. A Sudden Spike in Data Usage
Most mobile phone plans today offer a way to track your monthly data usage. If you typically use around 10GB of data a month, and suddenly you get an alert from your carrier that you have hit 50GB in just two weeks, you need to investigate immediately.
Spyware does not just record your private data; it has to send that data back to the hacker’s server. If a stalkerware app is secretly recording your conversations or taking background photos, it uses your cellular data to upload those massive files to the internet.
4. Ghost Apps Appear on Your Screen
This is the most obvious sign, yet many people ignore it. You swipe through your app drawer and notice an app with a generic name like “System Update,” “Battery Saver Pro,” or “Flashlight Plus.” You have absolutely no memory of downloading it.
Hackers often disguise malware under boring, system-like names hoping you will just assume it is an official part of the phone’s software. If you see an app you did not explicitly download, do not open it. Investigate it immediately.
5. Uncontrollable Pop-up Ads (Even on the Home Screen)
We all expect to see ads when browsing certain free websites. But if you are getting pop-up advertisements while you are navigating your phone’s settings menu, while reading a text message, or completely taking over your laptop’s desktop, your device is deeply infected with adware.
These pop-ups are often highly aggressive, featuring fake warnings like, “YOUR DEVICE HAS 13 VIRUSES! CLICK HERE TO CLEAN NOW.” (Never click those links; they will install even more malware).
6. Sluggish Performance and Constant Crashing
Remember how fast your device was when you first bought it? Apps snapped open instantly, and web pages loaded in a blink. If your device has suddenly become agonizingly slow—if it takes ten seconds just to open your contacts list, or if apps constantly freeze and crash back to the home screen—malware could be eating up all your available Random Access Memory (RAM).
7. Settings Changing on Their Own
Malware often needs to lower your device’s security shields to do its dirty work. If you notice that your laptop’s built-in antivirus (like Windows Defender) has been mysteriously turned off, or if your phone’s “Install from Unknown Sources” permission has been enabled without your knowledge, a malicious script is manipulating your system.
8. Unexplained Outgoing Calls or Texts
Many mobile trojans are designed to generate revenue for hackers by secretly sending premium-rate SMS messages from your phone. Check your sent messages folder and your monthly phone bill. If you see strange text messages sent to weird short-code numbers, or international phone calls you never made, malware is hijacking your cellular connection.
9. The Camera or Microphone Light Randomly Activates
In recent years, Apple and Google introduced a brilliant privacy feature: a tiny green or orange dot appears at the top of your screen whenever an app is actively using your camera or microphone.
If you are just reading an article or looking at your home screen, and that indicator light suddenly turns on, it means an app is secretly watching or listening to you. This is a massive, screaming red flag for stalkerware.
10. Your Browser is Hijacked
You open Google Chrome or Safari, type in a search query, but instead of taking you to Google, your browser redirects you to a strange, unfamiliar search engine filled with sponsored links. Or, you notice new toolbars installed at the top of your browser that you cannot seem to remove. Browser hijackers are a very common form of malware designed to track your web history and steal advertising revenue.
Part 3: Deep Dive Diagnostics – Smartphone Specifics
Now that we know the universal signs, let us look at how to properly diagnose the specific operating systems. Smartphones handle apps very differently than computers, so the investigation process is unique.
Diagnosing an Android Device
Android’s open-source nature gives users a lot of freedom, but it also makes it a larger target for malware, especially if you download apps from outside the official Google Play Store (sideloading).
- Check Data Usage by App: Go to Settings > Network and Internet > Mobile Network > App Data Usage. Scroll through the list. If you see an app you barely use (or do not recognize) consuming gigabytes of background data, that app is highly suspicious.
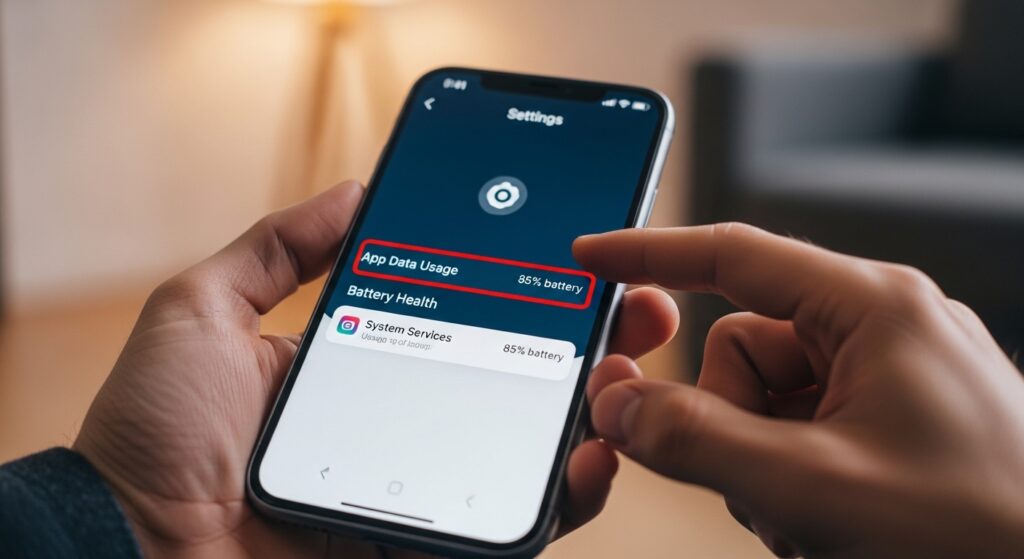
- Check Battery Usage by App: Go to Settings > Battery > Battery Usage. This list shows exactly what is draining your power. If a generic-sounding app is at the top of the list, ahead of your screen and heavy apps like YouTube, you have found the culprit.
- Review Device Admin Apps: Hackers use this hidden menu to prevent you from deleting their malware. Go to Settings > Security > Device Admin Apps. The only apps here should be official tools like “Find My Device” or Google Pay. If a flashlight or calculator app has Admin privileges, it is 100% malware.
Diagnosing an iPhone (iOS)
Apple’s iOS is a “walled garden.” It is extremely difficult (though not impossible) for traditional malware to infect an iPhone unless the phone has been “Jailbroken.” However, iPhones are still highly susceptible to phishing profiles and stalkerware installed by someone who knows your passcode.
- Check for Unknown Profiles: This is how hackers bypass the App Store to install spyware on iPhones. Go to Settings > General > VPN & Device Management. If you see a “Configuration Profile” installed here that you did not explicitly approve for work or school, someone has compromised your phone. Delete it immediately.
- Review Battery Health: Go to Settings > Battery and scroll down to see the list of apps consuming power. Look for any anomalies.
- Check Privacy Reports: Go to Settings > Privacy & Security > App Privacy Report. This brilliant feature shows you exactly which apps have accessed your location, camera, microphone, and contacts over the last 7 days. If a seemingly innocent app is constantly pinging your location, investigate it.
Part 4: Deep Dive Diagnostics – Laptop and PC Specifics
Computers are the traditional battleground for cybercriminals. Because we use laptops for deep financial work, coding, and heavy browsing, the malware here is often much more sophisticated.
Diagnosing a Windows PC
Windows is the most targeted operating system in the world.
- The Task Manager Test: Press Ctrl + Shift + Esc to open the Task Manager. Click on the “Processes” tab and sort by “CPU” or “Memory.” If your computer is running slowly, look at the top of the list. If a program you do not recognize is using 80% of your CPU, right-click it and select “Search online” to see if the internet identifies it as malware.
- Check Startup Programs: In the same Task Manager, click the “Startup” tab. These are the programs that launch silently the second you turn on your computer. If you see strange, publisher-less programs set to “Enabled,” disable them immediately.
- Run a Windows Defender Offline Scan: Go to Settings > Privacy & Security > Windows Security > Virus & threat protection > Scan options. Choose “Microsoft Defender Offline scan.” This reboots your computer and scans for deeply hidden rootkits before the Windows operating system fully loads.
Diagnosing a Mac (macOS)
Macs are not immune to viruses, despite the old marketing myths. Adware and browser hijackers are extremely common on macOS.
- The Activity Monitor Test: Open Spotlight (Command + Space) and type Activity Monitor. This is Apple’s version of the Task Manager. Sort by the “% CPU” column. Look for weird, unnamed processes eating up processing power.
- Check Login Items: Go to System Settings > General > Login Items. Review the list of applications that open automatically when you log in. Click the minus (-) button to remove anything suspicious.
- Check Safari Extensions: Open Safari, go to Preferences > Extensions. Malicious extensions are the number one cause of pop-up ads and browser redirects on Macs. Uninstall any extension you do not specifically remember installing.
Part 5: How Did the Malware Get There? (The 4 Entry Points)
Understanding how you got infected is crucial to ensuring it never happens again. Malware rarely hacks its way into your device by brute force; 99% of the time, the user accidentally invites it in.
- Phishing Links and Fake Emails: You receive an urgent email from a “shipping company” claiming a package could not be delivered, asking you to click a link to track it. You click the link, download a “tracking receipt,” and unwittingly install a trojan.
- Trojan Horse Apps: You want to watch a movie for free, so you search the web and download a shady video player app. The app actually plays the movie, but quietly installs spyware in the background.
- Malicious Email Attachments: Opening an innocent-looking PDF or Microsoft Word document from an unknown sender can trigger a hidden script (called a macro) that downloads ransomware onto your PC.
- Physical Access (The Stalkerware Route): If you leave your phone unlocked on the kitchen counter, it only takes a jealous partner or a nosy roommate two minutes to open a secret browser window and install hidden tracking software. This is why a strong screen lock passcode is non-negotiable.
(Note: If you want to learn more about securing your accounts from these entry points, check out our guide on Why You Need Two-Factor Authentication in 2026.)
Part 6: The Exorcism – How to Remove Malware Safely
If you have gone through the diagnostics and realized your device is undoubtedly infected, do not panic. Do not throw the device away. Follow this emergency removal protocol.
Step 1: Disconnect from the Internet
The first thing you must do is sever the hacker’s connection to your device. If it is a phone, turn on Airplane Mode. If it is a laptop, turn off the Wi-Fi or unplug the ethernet cable. This stops spyware from transmitting your data and prevents ransomware from receiving encryption commands from its master server.
Step 2: Boot into Safe Mode
Safe Mode starts your device with only the bare minimum, essential system files. It prevents all third-party apps (including the malware) from running.
- Android: Press and hold the power button. When the power menu appears on the screen, tap and hold the “Power Off” icon until the “Reboot to Safe Mode” prompt appears.
- Windows PC: Hold the Shift key while clicking “Restart” from the Start menu. Go to Troubleshoot > Advanced options > Startup Settings > Restart. Press 4 or F4 to boot into Safe Mode.
- Mac: Restart your Mac and immediately press and hold the Shift key until the Apple logo appears.
Step 3: Hunt and Destroy
While in Safe Mode, you have the upper hand. The malware is asleep.
- On Phones: Go to your app settings and uninstall the suspicious apps you identified earlier. If the “Uninstall” button is greyed out, remember to go to Security Settings and remove the app’s “Device Admin” privileges first.
- On Computers: Go to your Control Panel or Applications folder and uninstall the shady programs.
Step 4: Run a Premium Anti-Malware Sweep
Once you have manually removed what you can, reboot the device normally (turn off Safe Mode) and immediately run a deep system scan using a trusted, premium anti-malware tool.
- Do not use free, random cleaners you find on the internet (they are often malware themselves). Use reputable giants like Malwarebytes, Bitdefender, or Norton.
Step 5: The Nuclear Option (Factory Reset)
If your device is still acting possessed, or if you were infected with highly invasive stalkerware and you cannot trust the device anymore, it is time for the nuclear option: The Factory Reset.
A factory reset wipes the entire hard drive clean, deleting all photos, contacts, apps, and the operating system’s custom settings, returning the device to the exact state it was in when you bought it out of the box.

- Warning: Do not restore from a backup created after you noticed the weird behavior, or you will just reinstall the malware! Back up your important photos manually to a cloud drive, write down your contacts, and start completely fresh.
Part 7: Building the Fortress – Prevention for 2026
Removing malware is stressful and time-consuming. The golden rule of cybersecurity is that prevention is infinitely easier than a cure. Here is how you lock down your digital life moving forward:
- Never Click Blindly: Treat every link in a text message or email with extreme suspicion. If your bank texts you, do not click the link; open the official banking app yourself.
- Keep Everything Updated: Those annoying software update notifications are actually critical security patches closing loopholes that hackers exploit. Turn on automatic updates. Read our 10 Essential Tips to Secure Your Smartphone for more deep dives into device hardening.
- Use a Password Manager: Stop reusing “Password123”. A password manager creates impossible-to-crack passwords for every site you use.
- Lock Your Phone Screen: Never leave your phone unlocked in public, at work, or even around people you casually date. A strong 6-digit pin and biometric locks are your first defense against stalkerware.
- Use a VPN on Public Wi-Fi: If you work from coffee shops or airports, a Virtual Private Network encrypts your connection so hackers on the same network cannot intercept your data.
Frequently Asked Questions (FAQs)
Q1: Can an iPhone get a virus from visiting a website? It is extremely rare for an iPhone to get a traditional “virus” just from scrolling a web page. However, shady websites can flood your Safari calendar with spam invites, or use malicious pop-ups that lock your browser, tricking you into calling a fake tech support number. Clearing your Safari history usually fixes this.
Q2: Will a factory reset remove police or government spyware? Standard factory resets remove 99% of commercial stalkerware and malware. However, advanced military-grade spyware (like Pegasus) used by nation-states can sometimes survive a factory reset. If you are a high-risk target (journalist, politician), professional forensic analysis is required.
Q3: Are free Antivirus apps on the Google Play Store safe? Be very careful. Many free “Antivirus & Cleaner” apps on the Play Store are actually adware in disguise. They pretend to scan your phone, show fake warnings, and force you to watch ads to “clean” them. Always stick to established, paid cybersecurity brands.
Conclusion: Take Back Control of Your Tech
In 2026, realizing your device is infected with malware feels like discovering a stranger has been walking around your house while you sleep. It is a profound violation of privacy.
But you are not powerless. Cyber criminals rely on user ignorance. They hope you will ignore the fast-draining battery, blindly accept the weird pop-ups, and keep using the device while they extract your data.
By understanding the red flags—the heat, the ghost apps, the data spikes—you turn on the lights and catch them in the act. If you suspect an infection today, do not wait. Turn on Airplane Mode, enter Safe Mode, and take out the digital trash.
Your smartphone and laptop hold your entire life. It is time to start protecting them like it.

